Brute Force vs Dictionary Attack: What Every User Needs to Know
Published: 9 May 2026
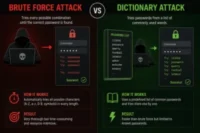
When it comes to password cracking and unauthorized system access, two of the most common methods used in cybersecurity are brute force vs dictionary attack techniques. These methods are often compared in discussions like dictionary attack vs brute force attack because they both target passwords, but they work in completely different ways.
A brute force attack vs dictionary attack comparison is important because one relies on testing every possible combination, while the other focuses on lists of common passwords and predictable patterns. This difference directly affects speed, success rate, and how attackers gain unauthorized access to systems.
With weak password practices still widespread, understanding how brute force attacks and dictionary-based attacks work is critical for improving security. This guide breaks down both methods, explains their differences, and shows how users can protect themselves using strong passwords and modern security practices.
Table of Contents
What Is a Brute Force Attack?
A brute force attack is a password cracking technique where an attacker tries every possible combination of characters until the correct password is found. The simplest way to understand it is to imagine someone trying every key on a large keyring, one by one, until the right one finally opens the lock.
This method works on a very basic principle: trial and error. There is no intelligence, no guessing strategy, and no shortcut involved. The system simply starts with simple combinations and continues testing letters, numbers, and symbols until it either finds the correct password or exhausts all possible options.
In theory, a brute force attack will always succeed if enough time and computing power are available. However, in real-world situations, that “enough time” quickly becomes unrealistic. Modern strong passwords, especially those that are long and include a mix of uppercase letters, lowercase letters, numbers, and symbols, can take an extremely long time to crack—even with powerful machines.
One of the most common signs of a brute force attack is a large number of failed login attempts. Because the process involves repeated guessing, it often triggers security systems that monitor unusual activity. Many platforms use intrusion detection systems to identify and block this type of behavior before any serious damage is done.
From a security perspective, brute force attacks are most effective against weak passwords or systems that lack proper protections like account lockouts or rate limiting. This is why password strength and system-level defenses play such an important role in preventing unauthorized access.
Key characteristics of brute force attacks:
- No prior knowledge of the password is required
- Works by trying every possible combination systematically
- Theoretically guaranteed success, but often impractical in real time
- Becomes significantly harder as password complexity increases
- Produces a high number of failed login attempts, making detection easier
- Commonly used against weak passwords, PIN codes, and basic encryption systems
What Is a Dictionary Attack?
A dictionary attack employs a more sophisticated approach. Instead of cycling through every possible combination, the attacker uses lists of common passwords, words from actual dictionaries, leaked credential databases, and known phrases to narrow down the guesses significantly.
The reasoning is simple: most people use predictable passwords. Words like “password,” “iloveyou,” “welcome1,” or names of sports teams remain among the most widely used credentials year after year. A dictionary attack targets this human tendency by prioritizing those common passwords before attempting anything else.
Modern dictionary attacks go further than static word lists. They incorporate password mutation rules, swapping letters for numbers (like “p@ssw0rd”), appending birth years, and combining two common words. This makes them far more effective against people who think they have made their password clever when they have really just followed a predictable substitution pattern.
Key characteristics of dictionary attacks:
- Relies on precompiled word lists and leaked credential databases
- Far faster than brute force for predictable passwords
- Ineffective against truly random, unique passwords
- Can be customized to reflect the target’s personal information
- Often used to gain unauthorized access to accounts at scale
Brute Force Attack vs Dictionary Attack: Key Differences
Protecting systems and personal accounts from both brute force vs dictionary attack methods requires a mix of simple habits and proper security controls. Since these attacks work differently, no single fix is enough on its own.
The most effective starting point is using strong passwords that are long, unique, and difficult to guess. Avoiding weak passwords such as names, birthdays, or common patterns significantly reduces the risk of both brute force and dictionary-based attempts. Most attacks succeed not because of advanced tools, but because of predictable choices made by users.
Another essential layer is multi-factor authentication (MFA). Even if a password is exposed or guessed, MFA adds an extra step that blocks unauthorized access. This makes it one of the most reliable defenses against both automated login attempts and large-scale password cracking methods.
System-level protections are also very important. Many platforms use account lockout mechanisms after repeated failed login attempts. This stops automated tools that rely on continuous guessing and makes both brute force and dictionary attacks far less effective.
Key protective measures include:
- Using strong, unique passwords for every account
- Avoiding common passwords and predictable patterns
- Enabling multi-factor authentication (MFA) wherever possible
- Allowing account lockout after multiple failed login attempts
- Monitoring unusual activity through intrusion detection systems
- Limiting repeated attempts from the same IP address
Security monitoring adds another layer of defense. Modern systems track unusual patterns such as repeated failed logins or suspicious spikes in traffic. These signals are often caught early by intrusion detection systems, which can block or alert administrators before any real damage occurs.
From a user perspective, checking password strength is a simple but effective habit. An AI Password Strength Tester can help identify predictable passwords and highlight weaknesses before attackers can exploit them through brute force or dictionary-based attacks.
Finally, using unique passwords across all accounts ensures that even if one credential is exposed, it cannot be reused elsewhere. Attackers often rely on reused credentials or lists of common passwords, so uniqueness remains one of the strongest defenses available.
Dictionary Attack vs Brute Force, Which Is Faster?
Both brute force vs dictionary attack methods are actively seen in real-world cybersecurity incidents, but they are used in slightly different ways depending on the target and objective.
One of the most common examples related to dictionary-based methods is credential stuffing. In this type of attack, cybercriminals use leaked username and password combinations from previous data breaches and try them across multiple platforms. Since many users reuse the same common passwords, these automated login attempts often succeed without needing to break encryption or guess anything new. At scale, this behaves very similarly to a dictionary attack, just applied across thousands of accounts and services.
Brute force attacks, on the other hand, are more commonly seen in targeted scenarios. These are often used against encrypted files, archives, or systems that do not have proper protections like account lockout or rate limiting. For example, attackers may try to crack Wi-Fi passwords or offline data files by systematically trying all possible combinations until one works.
In some cases, attackers combine both approaches. They may start with known or predictable password lists (dictionary-style guessing) and then switch to full brute force if those attempts fail. This hybrid approach increases the chances of success while saving time and computing resources.
Security professionals and ethical hackers also use these techniques in controlled environments. Penetration testers often simulate both brute force and dictionary-based attacks to identify weak login attempts, exposed credentials, or weak password policies before real attackers can exploit them.
Real-World Use Cases in Cybersecurity
Both attack types appear regularly in actual security incidents. Credential stuffing attacks, which flood services with stolen username and password combinations from previous data breaches, are essentially dictionary attacks at massive scale. Attackers buy or download leaked databases and use them to attempt login attempts across hundreds of services, betting that people reuse their passwords.
Brute force methods appear more often in targeted attacks, particularly against encrypted files, archived documents, or systems with no account lockout policy in place. Wi-Fi network cracking, for instance, often combines both methods, starting with common passphrase lists before falling back to exhaustive brute force.
Penetration testers and ethical hackers use both techniques as well, often running them against client systems with permission to identify weak spots before a real attacker does.
How Attackers Exploit Weak Passwords
Weak passwords make both brute force vs dictionary attack methods much more effective. When users choose passwords based on personal details, keyboard patterns like “qwerty,” or commonly used phrases, they unintentionally make it easier for attackers to guess them.
Both brute force and dictionary attack strategies take advantage of the same issue: people are not good at creating truly random passwords. We naturally choose something easy to remember, but attackers rely on that behavior. Even passwords that look “clever,” like “M@nch3ster1995,” can often be cracked using advanced dictionary-based techniques in a short time.
Attackers don’t always target one account at a time. In many cases, they automate login attempts across thousands or even millions of accounts. This makes large-scale attacks harder to notice at an individual level, although security systems can still detect unusual patterns using intrusion detection systems.
How to Protect Against Brute Force and Dictionary Attacks
Use Strong, Unique Passwords
The most direct defense is also the most obvious: use genuinely strong passwords that are long, random, and unique for every account. A password manager handles this automatically, generating credentials that neither brute force nor dictionary attacks can realistically crack within any useful timeframe.
Enable Multi-Factor Authentication
Multi-factor authentication (MFA) is arguably the most powerful single step anyone can take. Even if an attacker successfully cracks a password, they cannot access the account without the second factor, whether that is a one-time code, a hardware key, or a biometric check. MFA effectively nullifies the value of a cracked password in most scenarios.
Implement Account Lockout Policies
Systems that enforce account lockout after a set number of failed login attempts dramatically slow down both attack types. If an account locks after five incorrect attempts, an automated tool cycling through thousands of guesses per minute is quickly rendered ineffective. Temporary lockouts rather than permanent ones also reduce the support burden from accidental lockouts.
IP-Based Rate Limiting and Monitoring
Restricting the number of login attempts from a single IP address within a short period prevents automated tools from operating at the speed they need to be effective. Modern intrusion detection systems can flag unusual patterns, alert security teams, and automatically block suspicious sources before significant damage is done.
Enforce Strong Password Policies
Organizations should require complex passwords and actively block the use of known common passwords through blocklists. Forcing users away from predictable passwords reduces the effectiveness of dictionary attacks dramatically, even before other defenses come into play.
Comparison Table: Dictionary Attack vs Brute Force Attack
| Factor | Brute Force Attack | Dictionary Attack |
| Method | Tries every possible combination | Uses precompiled word lists and known passwords |
| Speed | Slow against complex passwords | Fast against weak or common passwords |
| Required knowledge | None | Word lists, leaked databases |
| Success rate | Guaranteed (given time); low for strong passwords | High for predictable passwords; zero for random ones |
| Resource intensity | Very high | Low to moderate |
| Detectable? | Yes — generates massive failed login volume | Somewhat — can be spread across accounts or IPs |
| Best defense | Long, complex passwords; account lockout | Unique passwords; blocklists; MFA |
| Common use cases | Encryption cracking, PIN attacks, Wi-Fi passwords | Credential stuffing, account takeovers at scale |
Conclusion
The brute force vs dictionary attack comparison reveals two distinct philosophies in password cracking. Brute force is relentless and all-encompassing. Dictionary attacks are surgical and efficient. Together, they represent the two most common ways attackers attempt to gain unauthorized access to accounts and systems.
The good news is that the defenses are well understood. Unique passwords, multi-factor authentication (MFA), account lockout policies, and consistent monitoring of failed login attempts form a layered security posture that makes both attack types impractical against well-protected accounts.
The weakest link in every scenario is still the human one. When users choose weak passwords out of convenience, they do the attacker’s job for them. When they choose genuinely strong passwords and enable MFA, they remove almost all of the attacker’s advantage. That choice, more than any technology, is what separates a secure account from a vulnerable one.
Frequently Asked Questions
What is the difference between a brute force vs dictionary attack?
The fundamental dictionary attack vs brute force attack differences lie in their approach. Brute force tries every possible combination systematically, while a dictionary attack limits its guesses to known words, phrases, and previously leaked passwords. Dictionary attacks are faster but less comprehensive. Brute force is exhaustive but slow.
Which attack is more dangerous?
It depends on the target. Dictionary attacks are more dangerous against accounts with predictable passwords because they succeed quickly and at scale. Brute force attacks are more dangerous in scenarios where an attacker has persistent, undetected access to a system and time to spare, such as cracking an offline encrypted file.
Can multi-factor authentication stop both attacks?
Yes, in most cases. Multi-factor authentication (MFA) ensures that even a successfully cracked password does not give an attacker access. It is one of the most reliable defenses against both force and dictionary attacks combined.
What is the difference between brute force vs dictionary attack in simple terms?
Brute force is like trying every possible lock combination from 0000 to 9999. A dictionary attack is like trying only the combinations that people commonly choose, such as their birth year or their pet’s name. One is thorough but slow; the other is fast but limited.
Does account lockout fully prevent these attacks?
Account lockout is a strong deterrent, but not a complete solution on its own. Sophisticated attackers may spread attempts across many accounts slowly to avoid triggering lockouts, or may target systems where lockout policies are not enforced. Pairing lockout policies with MFA, strong IP address monitoring, and good password hygiene provides the most layered protection.
Is a dictionary attack a brute force attack?
Not exactly. A dictionary attack is a smarter, faster variation that uses lists of common passwords rather than trying every possible combination. Brute force is exhaustive and methodical. Both aim to crack passwords, but they work very differently.
What is the most common hacked password?
“123456” consistently tops the list of most compromised passwords worldwide, followed by “password,” “12345678,” and “qwerty.” These appear in millions of breached accounts and are the first targets of any dictionary attack.

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks