What is Birthday Attack in Cryptography and Network security
Published: 5 May 2026
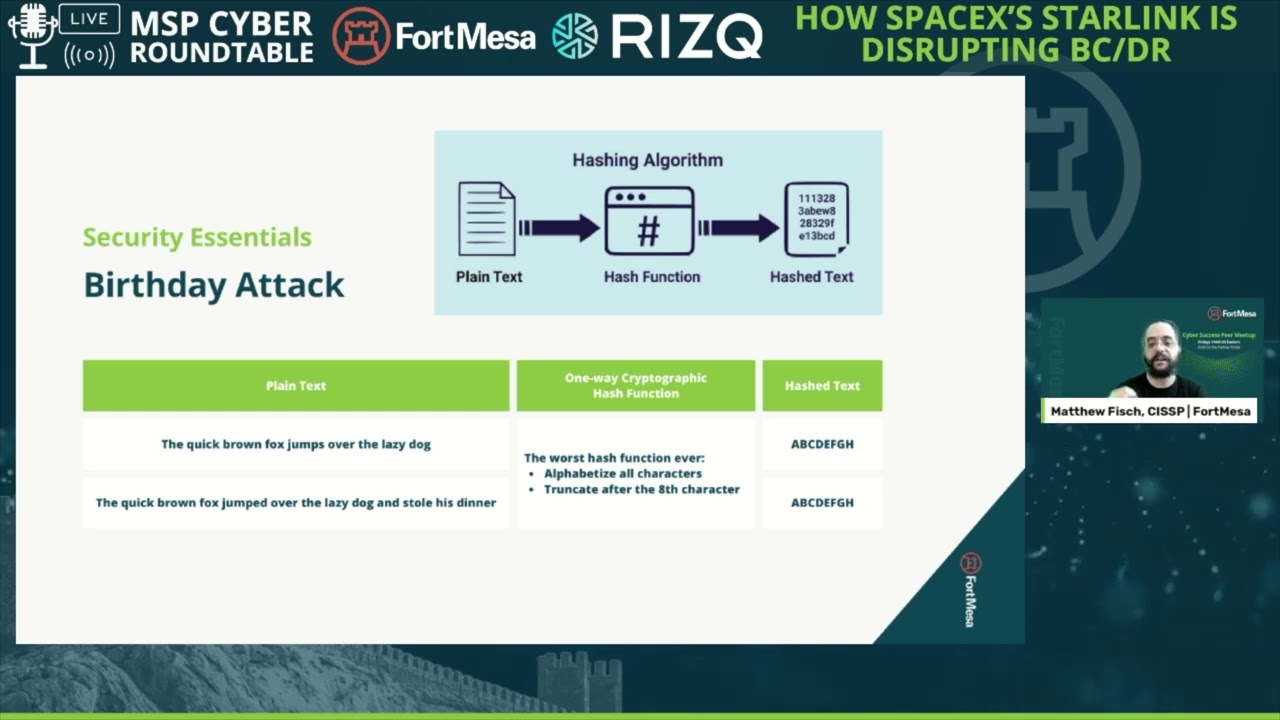
A birthday attack in cryptography finds collisions by generating different inputs that produce the same hash. It works by increasing the number of attempts until two outputs match, which happens faster than most expect.
In cryptography and network security, this technique targets hash functions like MD5 and SHA-1. A birthday attack in cryptography is an example that involves two different files ending up with identical hashes, allowing altered data to pass verification.
This pattern defines the birthday attack problem in cryptography and shows why modern systems rely on stronger algorithms such as SHA-256.
Table of Contents
What is a Birthday Attack?
A birthday attack is a method used to find two different inputs that produce the same hash value. It relies on probability, not on matching a specific output.
What is a birthday attack in simple terms? The attacker generates multiple inputs and looks for any pair that shares the same hash. This makes the attack faster than brute force methods.
What is a Security Attack in Cryptography and Network Security?
A security attack in cryptography targets data confidentiality, integrity, or availability by exploiting system weaknesses.
In cryptography and network security, attacks fall into two types. Passive attacks observe data without changes. Active attacks modify data or inject false information into the system.
A birthday attack in cryptography and network security is an active attack. It targets hash functions and forces collisions between different inputs. The attacker does not need the original data. The attacker only needs matching hash outputs.
This behavior makes collision-based attacks difficult to detect because the system processes both inputs as valid.
What is a Birthday Attack in Cryptography?
A birthday attack in cryptography finds two different inputs that produce the same hash value. It targets collision resistance, not a specific output, which reduces the effort needed compared to brute force methods.
In cryptography and network security, this attack focuses on hash functions that map large inputs into fixed-length outputs. When two inputs share the same hash, systems treat them as identical, even when the data differs.
Why Does Birthday Attack in Cryptography Work?
A birthday attack works because collision probability increases faster than expected as the number of inputs grows. This effect comes from the birthday paradox, where shared outcomes appear with fewer attempts than intuition suggests.
This is known as the birthday attack problem in cryptography. For a hash space of size N, a collision becomes likely after about √N attempts, not N attempts.
Birthday Attack in Cryptography Example
A birthday attack in cryptography example involves two different files generating the same MD5 hash.
- File A → original content
- File B → modified content
- Hash(A) = Hash(B)
Systems that rely only on hash comparison accept both files as valid. This weakness allowed attackers to exploit MD5 in real-world scenarios.
How Does Birthday Attack Probability Work?
A birthday attack reaches a 50% collision probability after about 1.2 × √N attempts, not N. This rapid increase comes from pairwise comparisons between inputs, not individual matches against a fixed hash.
Birthday Attack Probability Formula
The probability of at least one collision follows this model:
- P ≈ 1 − e^(-k² / 2N)
- k → number of generated inputs
- N → total hash space size
As k increases, the number of possible pairs grows as k(k−1)/2, which drives collision probability upward.
Birthday Attack Complexity Explained
A birthday attack in cryptography reduces computational effort to O(√N).
| Method | Attempts Required | Goal |
| Brute Force | O(N) | Match exact hash |
| Birthday Attack | O(√N) | Find any collision |
Collision Probability by Hash Size
| Hash Size (bits) | Hash Space (N) | ~50% Collision Attempts |
| 64-bit | 2⁶⁴ | 2³² |
| 128-bit (MD5) | 2¹²⁸ | 2⁶⁴ |
| 160-bit (SHA-1) | 2¹⁶⁰ | 2⁸⁰ |
| 256-bit (SHA-256) | 2²⁵⁶ | 2¹²⁸ |
Shorter hashes reduce the work needed for a successful birthday attack in cryptography, which explains why older algorithms fail under collision-based attacks.
You will now see how this probability directly affects the security and collision resistance of hash functions.
Why Are Hash Functions Vulnerable to Birthday Attacks in Cryptography?
Hash functions become vulnerable when their output size allows feasible collision discovery using O(√N) attempts. The smaller the hash length, the easier it becomes to generate two inputs with the same hash.
In a birthday attack in cryptography, the attacker does not break the hash function directly. The attacker exploits the fixed output size and collision probability.
What is Collision Resistance?
Collision resistance is a property that prevents two different inputs from producing the same hash.
- Strong collision resistance → collisions are computationally infeasible
- Weak collision resistance → collisions can be generated in practical time
A birthday attack in cryptography and network security directly targets this property.
Hash Length vs Collision Risk
| Hash Algorithm | Output Size | Collision Effort | Status |
| MD5 | 128-bit | 2⁶⁴ | Broken |
| SHA-1 | 160-bit | 2⁸⁰ | Deprecated |
| SHA-256 | 256-bit | 2¹²⁸ | Secure |
| SHA-3 | 256+ bit | ≥2¹²⁸ | Secure |
Is SHA-256 Safer than MD5?
Yes. SHA-256 is safer than MD5 because it uses a 256-bit output, which increases collision resistance to 2¹²⁸ operations. MD5 uses a 128-bit output, making collisions achievable with far fewer resources.
This difference is why modern systems avoid older hash functions when facing a birthday attack in cryptography scenarios.
Next, you will see how these weaknesses were exploited in real-world attacks.
Real-World Birthday Attack in Cryptography and Network Security
Real systems failed when attackers generated practical hash collisions. A birthday attack in cryptography and network security moved from theory to execution once collision costs dropped within reachable computational limits.
Birthday Attack on MD5
Attackers produced MD5 collisions in 2004, showing the hash no longer ensured integrity.
- Researchers: Xiaoyun Wang et al.
- Collision effort: ~2⁶⁴ operations (reduced further with optimizations)
- Real use case: Rogue SSL certificate (2008)
| Attribute | Details |
| Hash Algorithm | MD5 |
| Output Size | 128-bit |
| Attack Type | Collision (Birthday attack) |
| Status | Broken |
A birthday attack in cryptography example here involves two certificates with different contents but identical hashes, allowing a trusted signature to validate a malicious certificate.
Birthday Attack on SHA-1
SHA-1 replaced MD5 but failed under similar pressure. In 2017, Google and CWI Amsterdam demonstrated a practical collision.
- Project: SHAttered
- Collision cost: ~2⁶³ operations
- Method: Chosen-prefix collision attack
| Attribute | Details |
| Hash Algorithm | SHA-1 |
| Output Size | 160-bit |
| Attack Type | Collision (Birthday attack) |
| Status | Deprecated |
This attack confirmed that even stronger hashes become vulnerable when collision resistance weakens under the birthday attack in cryptography conditions.
Next, you will compare birthday attacks with other attack methods to understand their efficiency differences.
What is the Difference Between Birthday Attack and a collision attack?
A birthday attack is a method used to find collisions, while a collision attack is a broader category that includes any technique that produces identical hash outputs.
- Collision attack → goal: find two inputs with the same hash
- Birthday attack → method: uses probability to achieve that goal
| Concept | Scope | Approach |
| Collision Attack | Broad | Any collision method |
| Birthday Attack | Specific | Probability-based method |
A birthday attack in cryptography is one of the most efficient ways to perform a collision attack because it reduces the number of required attempts.
What is the Difference Between Brute Force Attack and a birthday attack?
A brute force attack searches for a specific hash match, while a birthday attack searches for any matching pair of hashes.
| Attack Type | Complexity | Objective |
| Brute Force | O(N) | Exact hash match |
| Birthday Attack | O(√N) | Any collision |
In cryptography and network security, this difference matters because a birthday attack in cryptography succeeds faster when collision resistance is weak.
Next, you will see how these attacks impact digital signatures and trust systems.
What is the Impact of Birthday Attack on Digital Signatures?
A birthday attack breaks digital signatures by creating two different documents with the same hash. One version stays harmless. The other carries modified content. Both produce identical hashes.
The attacker submits the harmless document for signing. The system generates a valid signature based on its hash. Later, the attacker replaces it with the modified document that has the same hash.
The signature still verifies because the hash matches. The system has no way to detect the change.
This is a direct result of the birthday attack in cryptography, where collision resistance fails. In real systems, this risk led to the deprecation of MD5 and SHA-1 for certificate signing.
Next, you will see how to prevent birthday attacks in cryptographic systems.
How to Prevent Birthday Attacks in Cryptography?
You prevent a birthday attack in cryptography by increasing collision resistance and limiting predictable hash usage.
Birthday Attack Mitigation Techniques
Use stronger hash functions with larger output sizes. A larger hash space increases the effort required for collisions.
- Use SHA-256 or SHA-3 instead of MD5 or SHA-1
- Avoid deprecated hashing algorithms in production systems
- Apply randomization (salting) where applicable
Collision resistance improves because attackers now need ~2¹²⁸ attempts instead of ~2⁶⁴.
Best Practices for Cryptographic Security
Security depends on correct implementation, not just algorithm choice.
- Use digital signature schemes with secure hash functions (e.g., RSA-PSS, ECDSA with SHA-256)
- Follow standards from NIST (FIPS 180-4, FIPS 202)
- Update cryptographic libraries regularly
In cryptography and network security, these steps reduce the feasibility of a birthday attack in cryptography by increasing computational cost beyond practical limits.
Next, you will explore learning resources such as PPTs and PDFs to visualize how birthday attacks work.
Final Thoughts
A birthday attack in cryptography works because collisions appear faster than expected as inputs increase. That single property made older hash functions like MD5 and SHA-1 unreliable in real systems.
In cryptography and network security, the risk is not theoretical. A birthday attack in cryptography example already showed how identical hashes can validate different data, which breaks trust mechanisms.
This is the core of the birthday attack problem in cryptography. Stronger algorithms such as SHA-256 reduce this risk by increasing collision resistance and pushing attack costs beyond practical limits.
Test your password: AI Password Strength Tester
FAQs
What is the birthday paradox in cryptography?
The birthday paradox in cryptography explains why hash collisions occur quickly as the number of inputs increases, forming the basis of a birthday attack.
What is a hash collision attack?
A hash collision attack finds two different inputs that produce the same hash value. A birthday attack is one method used to achieve this.
Can a birthday attack break encryption?
A birthday attack targets hash functions, not encryption algorithms. It affects data integrity, not confidentiality.
Why are hash collisions dangerous?
Hash collisions allow different inputs to produce the same output. Systems may accept altered data as valid, which breaks verification mechanisms.

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks