What Is Vishing Attack in Cyber Security: A Complete Guide
Published: 30 Apr 2026
A vishing attack is a voice-based social engineering attack where cybercriminals call targets while impersonating trusted entities, such as banks, government agencies, or IT departments, to extract sensitive information like passwords, account numbers, or personal identification details. Unlike attacks that rely on malware or network intrusions, vishing exploits human psychology directly, making it effective against even technically aware individuals.
The attack follows a predictable pattern: an attacker calls a target using a spoofed number, delivers a prepared script built around a false scenario, creates pressure or urgency, and walks away with credentials, money, or access. Modern vishing campaigns now use Voice over Internet Protocol (VoIP) systems, voice cloning powered by artificial intelligence (AI), and deepfake video calls to make these scenarios more convincing than ever.
This article covers what vishing is, how it differs from phishing and smishing (SMS phishing), the specific techniques attackers use, real examples of vishing in action, warning signs to watch for, and the concrete steps organizations and individuals can take to reduce their exposure.
Table of Contents
What is Vishing?
Vishing, short for voice phishing, is a type of social engineering attack conducted over phone calls, where an attacker impersonates a legitimate person or organization to manipulate a target into disclosing sensitive information or taking a harmful action.
The word itself combines “voice” and “phishing.” While phishing uses email and smishing uses text messages, vishing uses real-time voice conversation, which gives attackers a psychological advantage. A voice call creates immediacy. There is no time to verify, forward the message to a colleague, or check a link before responding. The attacker controls the pace of the interaction.
Vishing targets both individuals and organizations. An individual might receive a call from someone claiming to be their bank’s fraud department. An employee at a company might receive a call from someone posing as their IT helpdesk or an executive asking for urgent wire transfers. In both cases, the attacker needs only one thing: for the target to trust the voice on the other end long enough to comply.
What is the Difference Between Vishing, Phishing, and Smishing?
Phishing, smishing, and vishing are all forms of social engineering. All three aim to steal sensitive data or push targets into taking harmful actions. The difference lies in the delivery channel and the specific psychological tactics each uses.
Phishing
Phishing uses fraudulent emails to impersonate legitimate organizations, such as banks, government agencies, or well-known brands. The email typically contains a malicious link or an infected attachment. Clicking either gives the attacker access to credentials, financial data, or the victim’s system.
Phishing emails often carry a tone of urgency or alarm, telling recipients their account has been locked, a payment failed, or suspicious activity was detected. Because email remains the primary communication channel in most workplaces, phishing attacks reach a wide audience and can be scaled cheaply.
Smishing
Smishing uses SMS text messages to deliver the same kind of deceptive content. A smishing message might appear to come from a delivery company, a bank, or a coworker and typically includes a shortened link directing the recipient to a fake login page or a number to call.
Text messages are read faster and questioned less than emails. People tend to assume texts are personal and immediate, which smishing campaigns exploit. As mobile usage has grown, so have smishing attack volumes.
Vishing
Vishing operates through voice calls, either made by a live attacker or through an automated system. What makes vishing distinct is the real-time human element. A skilled attacker can adapt to responses, answer objections, and apply emotional pressure in ways that a static email or text message cannot.
Attackers use caller ID spoofing to make calls appear to originate from trusted numbers. They may impersonate bank representatives, IRS agents, tech support staff, or company executives. When AI voice cloning is involved, they can even replicate the actual voice of a known person.
Key Differences in Attack Vectors and Tactics
| Attack Type | Delivery Channel | Primary Tactic | Key Risk Factor |
| Phishing | Malicious links, infected attachments | Scale and reach across email inboxes | |
| Smishing | SMS/Text messages | Shortened URLs, fake login pages | Immediate trust associated with text messages |
| Vishing | Voice calls | Impersonation, real-time social pressure | Real-time manipulation, no time to verify |
Why Is Vishing a Growing Threat?
Several factors have combined to make vishing more common and more effective than it was a decade ago.
VoIP technology lowered the cost of making calls dramatically. An attacker no longer needs a physical phone line or a local presence. Calls can be made from anywhere in the world, in bulk, at minimal cost, with the caller ID displaying whatever number the attacker chooses. This removed the logistical barriers that once limited the scale of phone-based fraud.
At the same time, personal data has become easier to obtain. Social media profiles, data broker websites, corporate directories, and leaked databases give attackers enough information to build a convincing backstory before placing a call. When an attacker already knows a target’s name, employer, job title, and recent activity, the fabricated scenario they present sounds far more credible.
Remote work has also expanded the attack surface. When employees are not physically present in an office, they cannot walk down the hall to verify whether a call from “IT support” or “the CFO” is legitimate. The phone becomes the primary communication channel for many sensitive interactions, and that is exactly where vishing attacks land.
AI has accelerated all of this. Voice synthesis tools can clone a person’s voice from a few minutes of recorded audio. Natural language processing (NLP) allows automated systems to hold realistic conversations. Machine learning enables attackers to mine public data and build targeted attack profiles at scale. According to the Zscaler ThreatLabz 2024 Phishing Report, AI-driven phishing attacks, including vishing, increased by 60% over the past year.
In 2022, a doctor in South Korea lost $3 million in cash, insurance, stocks, and cryptocurrency to vishing attackers who impersonated regional law enforcement officials. In Hong Kong, a finance employee paid $25 million after a deepfake video call where the attacker impersonated the company’s chief financial officer (CFO), with other participants on the call also being deepfake recreations of real staff members.
How Vishing Works: Techniques and Tactics
Caller ID Spoofing
Caller ID spoofing allows attackers to manipulate what appears on the recipient’s phone screen. The displayed number might belong to a real bank branch, a government agency, or even a known colleague. This single step substantially increases how many targets pick up and engage with the call.
Traditional caller ID-based authentication is no longer reliable as a result. Seeing a familiar number on the screen means nothing if the call originates from a completely different source. Organizations need identity verification measures that go beyond matching a caller ID to a known number.
Pretexting
Pretexting is the construction of a false scenario, or “pretext,” that gives the attacker a plausible reason for calling. Common pretexts include a fake fraud alert from a bank, a supposed IT department calling about a security incident, a delivery company requesting reconfirmation of an address, or a government agency threatening legal action over unpaid taxes.
The effectiveness of pretexting depends on the attacker’s ability to make the scenario feel urgent and legitimate. A well-researched pretext, built on real details gathered from public sources, is significantly harder to dismiss. AI-driven behavior analysis tools can help detect the social engineering cues embedded in these scripts before they lead to a breach.
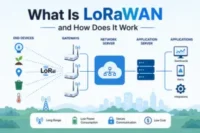
VoIP Exploitation
Voice over Internet Protocol (VoIP) systems allow attackers to place calls over the internet rather than traditional phone lines. VoIP is cheaper, more scalable, and easier to anonymize than conventional telephony. An attacker can route thousands of calls through VoIP infrastructure, using different spoofed numbers for each, making the campaign both cheap and difficult to trace.
VoIP platforms are also less regulated and often less secure than traditional telephone networks, which makes them a preferred tool in large-scale phishing operations.
Interactive Voice Response (IVR) Attacks
Interactive voice response (IVR) systems are the automated phone menus that organizations use for customer service and account access. Vishing attacks target IVR systems by directing victims to call a fraudulent number that mimics a legitimate IVR interface. Once on the call, the victim is prompted to enter sensitive information such as account numbers, PINs, or passwords, which the attacker captures.
Advanced threat detection systems can monitor IVR interaction patterns for anomalies and flag unusual inputs in real time.
Voice Cloning
AI-powered voice cloning allows attackers to replicate a specific person’s voice using only a short sample of recorded audio, sometimes as little as a few seconds taken from a public video or voicemail. The cloned voice can then be used in a call to impersonate that person convincingly.
This technique is particularly effective in business environments where an employee receives what sounds like a call from their CEO or a senior manager making an urgent request. The voice cloning vishing attack targeting Zscaler’s own CEO, Jay Chaudhry, in 2023 followed this exact pattern: an attacker used an AI-cloned version of Jay’s voice on WhatsApp to instruct a Zscaler employee to purchase gift cards, then quickly disconnected and followed up via text claiming poor network coverage. The employee reported it, and ThreatLabz investigators found it was part of a broader campaign targeting multiple tech companies.
Deepfake Video Calls
Beyond audio, AI can now generate deepfake video in real time, allowing an attacker to appear on a video call as someone else entirely. In remote work environments where video calls are standard, this is particularly effective. The target sees a familiar face, hears a familiar voice, and has no obvious reason to question the interaction.
The $25 million Hong Kong case mentioned earlier is one of the most documented examples of deepfake video call fraud at a corporate scale. The victim attended a multi-person video call and had no way to determine that every participant other than themselves was a fabricated deepfake.
Robocalls
AI-driven robocalls have evolved well beyond pre-recorded messages. Using NLP, modern robocall systems can engage in two-way conversation, responding to what the target says in a way that sounds natural. This allows a single attacker to run hundreds or thousands of simultaneous calls, filtering for targets who engage and escalating those interactions.
The scale possible with AI-driven robocalls means attackers can cast an extremely wide net while keeping per-target costs negligible.
AI Data Mining for Targeted Vishing
Before placing a call, sophisticated attackers use AI to mine publicly available data from social media platforms, corporate websites, professional networks, and leaked databases. This produces a profile of the target, including their name, role, colleagues, recent activities, and personal details, that makes the pretext far more convincing.
A vishing call that opens with accurate details about the target’s employer, manager, or recent transaction creates immediate credibility, reducing the target’s instinct to question the call’s legitimacy.
Multichannel Phishing-Vishing Attacks
Many modern attacks do not rely on a single channel. A common sequence starts with a phishing email that instructs the recipient to call a number to resolve an issue. The call connects to a vishing attacker or a convincing IVR system. In some variants, an initial smishing message drives the target to a fake website that then prompts a callback. These multichannel attacks use each channel to reinforce the others, making the overall deception harder to detect.
Vishing Examples
IRS Tax Scam
The attacker calls a target claiming to be an IRS agent, citing an unpaid tax debt and threatening immediate arrest or legal action unless payment is made through wire transfer, cryptocurrency, or gift cards. The calls often intensify around tax season. The IRS has confirmed publicly that the real agency does not initiate contact by phone and does not demand immediate payment without prior written notice.
Tech-Support Attacks
The caller claims to be from a well-known technology company’s support team, warning the target of a virus or security breach on their device. The attacker requests remote access to fix the problem. Once access is granted, the attacker either installs malware, steals stored credentials, or demands payment for the fake service.
Bank-Impersonation Scams
The caller poses as a fraud prevention officer at the target’s bank, claiming that suspicious transactions have been detected on their account. The target is asked to verify identity by providing account numbers, passwords, or one-time passcodes (OTPs) sent by the real bank. Those credentials then give the attacker access to the actual account.
Social Security or Medicare Scams
Attackers pose as officials from the Social Security Administration (SSA) or Medicare, claiming the target’s benefits have been suspended due to suspicious activity or an administrative issue. Older adults are disproportionately targeted. The caller requests personal identification numbers or payment to reinstate benefits.
Delivery Scams
The caller claims to represent a delivery company and states that a package is on hold due to a customs fee or failed delivery attempt. The target is asked to provide payment card details or personal information to release the package. These calls have increased significantly alongside the growth of e-commerce.
Loan and Investment Scams
Attackers pose as financial advisors or lending officers, offering unusually favorable loan terms or investment opportunities. They collect upfront fees, personal financial information, or account access, then disappear. Retirement accounts are a frequent target in investment-focused vishing attacks.
Voice-Cloning Vishing Scams
One widely reported scenario involves an attacker cloning the voice of a family member, calling a relative, and claiming to be in distress, often in a fabricated accident or legal trouble, and asking for immediate wire transfers. Because the voice sounds genuinely familiar, victims often comply before they think to call the actual family member independently.
The Tech Support Coworker
An employee receives a call from someone who sounds like an internal IT staff member. The caller knows the employee’s name, department, and the company’s internal systems, gathered through prior data mining. The caller claims an urgent security patch needs to be installed remotely and requests login credentials to proceed.
The Client
An attacker researches a business’s client list and calls an employee posing as one of those clients. Using details gathered from social media and the client’s public website, the attacker sounds credible enough to request a change to payment account details, redirecting future payments to a fraudulent account.
The Bank
An employee at a company receives a call from someone claiming to be their corporate bank’s fraud team. The caller references a recent large transaction, which was found through publicly available financial filings, and states the account has been temporarily frozen. To unfreeze it, the employee is asked to confirm account credentials and authorize a verification transfer.
Signs of Vishing
There are 8 consistent warning signs that a call may be a vishing attack:
- The caller creates urgency, insisting the target must act immediately to avoid a penalty, arrest, account closure, or financial loss.
- The caller requests sensitive information over the phone, including passwords, PINs, Social Security numbers, or payment card details.
- The caller ID shows a number from a bank, government agency, or known company, but the request being made does not match how that organization normally operates.
- The caller asks the target to stay on the line and not call anyone else, which is a deliberate attempt to prevent independent verification.
- The requested payment method is unusual, such as gift cards, cryptocurrency, or wire transfers to an unfamiliar account.
- The caller knows some personal details about the target but asks for more, using what they already know to build false trust.
- The call involves a recorded message directing the target to press a number or call back a specific number to resolve a problem.
- Something about the voice sounds slightly off, whether in pacing, tone, or response timing, which can indicate AI voice synthesis.
What to Do If You’ve Experienced a Vishing Attack
The steps to take after a vishing attack depend on what information was shared and how quickly the attack is identified.
Hang up immediately if the call is still ongoing. Do not provide any further information, regardless of how the caller responds or what threats they make.
If financial account details, passwords, or PINs were shared, contact the relevant institution directly using the official number on the back of a card or on the institution’s verified website. Report the incident and request a freeze or reset of the affected accounts.
If company credentials or internal system access were provided, report the incident to the organization’s IT or security team immediately. Speed matters. The sooner the security team knows, the faster they can revoke access and investigate the scope of what was exposed.
File a report with the relevant authority. In the United States, that includes the Federal Trade Commission (FTC) at reportfraud.ftc.gov and, if the call impersonated the IRS, the Treasury Inspector General for Tax Administration (TIGTA). In other countries, the appropriate national cybersecurity or consumer protection authority applies.
Document everything: the number that called, the time, what was said, and what information was shared. This detail is useful for investigators and for your own IT team.
Monitor affected accounts closely for any unauthorized transactions or access attempts in the days and weeks following the incident.
How to Prevent Vishing
Protect Accounts with Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) requires more than just a password to access an account. Even if an attacker obtains credentials through a vishing call, MFA creates an additional verification step, typically a time-sensitive code sent to a device, that the attacker cannot easily bypass. Deploying MFA across all critical accounts significantly reduces the damage a compromised password can cause.
Bolster Email Security with Threat Defense
Many vishing attacks start with an email directing the target to call a number or click a link that initiates a call. Deploying email security tools that scan for phishing indicators, suspicious links, and spoofed sender addresses reduces the number of targets who reach the phone-call stage of these multichannel attacks.
Avoid Answering Unsolicited Calls
Treat unsolicited calls from unknown numbers with suspicion by default. If a caller claims to represent a bank or government agency, hang up and call that organization back using the number listed on their official website. This single habit eliminates the risk from most pretexting scenarios.
Be Alert to Social Engineering Tactics
Awareness of how social engineering works is one of the most effective defenses. Vishing attackers rely on urgency, fear, and authority to override rational thinking. Recognizing these tactics in real time, and deliberately slowing down before complying with any request made over the phone, disrupts the attacker’s approach.
Ask for Proof of Identity
Any legitimate organization calling to request sensitive information will have a process for verifying their own identity, not just the caller’s. Ask the caller for their name, department, and a reference number, then call the organization back through official channels to verify. A legitimate caller will accept this; an attacker will resist or apply pressure.
Train Employees in Phishing Prevention
Regular security awareness training that covers vishing scenarios, not just email phishing, helps employees recognize attack patterns before they become victims. Training should include real examples, simulated vishing exercises, and clear protocols for what to do when a suspicious call is received.
Caller Authentication Procedures
Organizations should establish formal protocols for handling inbound calls that request sensitive information or system access. These protocols include callback verification, where the employee calls the requester back on a known number, and multi-person approval for high-risk actions such as wire transfers or credential resets.
Use of Anti-Spam Technology
AI-driven call-filtering and anti-spam technologies can screen inbound calls for patterns associated with robocalls and known vishing operations. These tools reduce the number of fraudulent calls that reach employees and flag suspicious caller profiles before the call is connected.
Incident Response Plans
A documented incident response plan for vishing attacks tells employees exactly what to do when they receive or fall for a suspicious call. Without this plan, response is slower, inconsistent, and more likely to miss critical steps like revoking access or notifying affected parties. The plan should include clear escalation paths, contact numbers for the security team, and post-incident review procedures.
AI Security and Threat Intelligence
AI-powered security platforms can detect unusual patterns in call behavior, flag known vishing infrastructure, and monitor for real-time threat intelligence around emerging attack campaigns. As attackers use AI to improve their attacks, defenders need AI-powered tools to identify those attacks at the speed and scale required.
Create Policies for Organizational Communications
Clear internal policies about how sensitive requests are made and approved close the gap that vishing attacks exploit. For example, a policy stating that no password reset will ever be initiated by an inbound call, or that any payment instruction must be verified through a second channel, removes the pretexts attackers depend on.
Limit the Potential Impact of Vishing
Apply the principle of least privilege to system access. Employees should only have access to the data and systems their role requires. If an attacker successfully tricks an employee into providing credentials, limiting that account’s access scope reduces how far the attacker can move within the organization’s systems.
Conclusion
A vishing attack is a direct, personal, and increasingly sophisticated form of social engineering that targets human judgment rather than software vulnerabilities. Attackers use caller ID spoofing, pretexting, VoIP exploitation, IVR attacks, voice cloning, deepfake video calls, AI-driven robocalls, and targeted data mining to build convincing scenarios that push targets into disclosing sensitive information or transferring funds.
The threat is growing because the tools that enable it, AI voice synthesis, cheap VoIP infrastructure, and abundant personal data, are all more accessible than they were just a few years ago. A 60% year-over-year increase in AI-driven phishing attacks, including vishing, confirms that this is not a static threat.
Defending against vishing requires combining employee training, strict caller authentication procedures, MFA deployment, AI-powered threat detection, and clear organizational policies. No single measure is enough on its own. The attacks are multifaceted, and the defenses need to match that complexity.
FAQs
What is Phishing?
Phishing is a cyberattack where criminals send fraudulent emails impersonating legitimate organizations to steal login credentials, financial data, or personal information. Phishing emails typically contain malicious links or infected attachments. The recipient is directed to a fake login page or prompted to download malware. Phishing remains one of the most common entry points for data breaches in both personal and corporate environments.
What is Smishing?
Smishing is a phishing attack delivered through SMS text messages, where attackers impersonate trusted sources to trick recipients into clicking malicious links or sharing sensitive information. Smishing messages often appear to come from banks, delivery companies, or government agencies and use shortened URLs to disguise their destination. The casual, immediate nature of text messaging makes recipients less likely to question the message before responding.
What is Email Security?
Email security refers to the policies, tools, and practices used to protect email accounts and communications from unauthorized access, phishing attacks, malware, and data interception. Email security solutions typically include spam filtering, malware scanning, anti-phishing controls, and encryption. Because phishing and multichannel vishing attacks frequently start with email, strong email security is a foundational layer in any organization’s cybersecurity posture.
What is Multi-Factor Authentication?
Multi-factor authentication (MFA) is a security process that requires users to verify their identity through two or more independent factors before accessing an account or system. Those factors typically combine something the user knows (a password), something the user has (a phone or hardware token), and sometimes something the user is (a biometric). MFA significantly reduces the risk of account compromise even when passwords are stolen through vishing or other attacks.
What is a Whaling Phishing Attack?
A whaling phishing attack is a highly targeted form of phishing directed at senior executives or high-value individuals within an organization, such as CEOs, CFOs, or board members. These attacks invest more effort in research and personalization than standard phishing campaigns. Whaling attacks often impersonate regulators, legal counsel, or other executives, and they frequently involve vishing as part of a multichannel approach. The financial and reputational stakes of a successful whaling attack are considerably higher than those of a generic phishing campaign.
What is Password Security?
Password security refers to the practices used to create, store, and protect passwords to prevent unauthorized access to accounts. Strong password security includes using long, unique passwords for each account, avoiding easily guessable information, storing passwords in an encrypted password manager, and changing passwords promptly following a suspected compromise. In the context of vishing, password security matters because one of the primary goals of a vishing call is to extract a password directly from the target.
What is Cybercrime?
Cybercrime is any criminal activity that involves a computer, network, or digital device, either as the tool used to commit the offense or as the target of it. Cybercrime includes vishing, phishing, smishing, identity theft, financial fraud, ransomware attacks, and unauthorized access to systems. Vishing sits within the broader category of cybercrime as a social engineering-based attack that exploits human behavior to gain unauthorized access to personal or organizational assets.

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks