Cybersecurity Explained: Concepts, Threats, Protection, and Careers
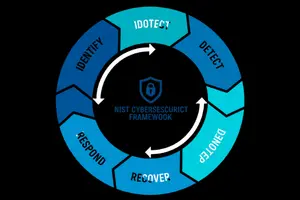
Cybersecurity is the discipline focused on protecting digital systems, networks, and data from cyber threats such as malware, data breaches, and unauthorized access. This cybersecurity hub provides structured explanations of core security concepts, including the CIA Triad, cryptography, access control models, and modern defense strategies such as Zero Trust Architecture.
Our content also covers threat intelligence, cloud and IoT security challenges, and the skills, roles, and career paths required in the cybersecurity field. Together, these guides help readers understand how cybersecurity works, why it is critical for modern organizations, and how digital defense continues to evolve.
Cybersecurity Articles
Cybersecurity Popular Title
Cybersecurity books for beginners are the perfect first step if you want to protect yourself online, explore ethical hacking, or prepare for a tech career. […]
It’s frustrating when you earn cybersecurity certifications, complete capture-the-flag (CTF) challenges, and practice penetration testing, yet employers still overlook your resume. A cybersecurity portfolio website […]
Why is your cybersecurity website still invisible on Google while competitors attract all the clicks? In an industry built on trust, compliance, and security, being […]
The digital world generates a vast amount of data, and companies must safeguard it. Hackers try to steal information every day, so businesses hire cyber […]
Cybersecurity protects the systems, data, and digital operations that organizations rely on every day. As businesses migrate to the cloud, adopt automation, and expand their […]
Using Kali Linux for penetration testing is essential for protecting systems from cyberattacks. Penetration testing is testing your website or network by pretending to be […]